New WordPress Hack Delivers Ransomware to Site Visitors
WordPress Hack through a Ransomware
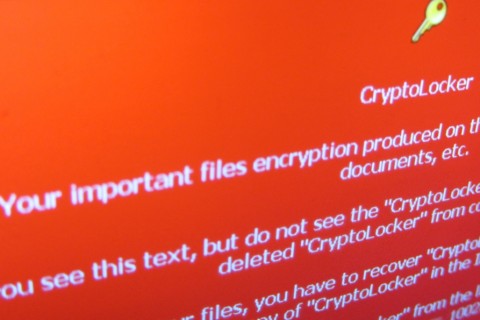
Malicious attacks are fairly common on shady websites. Staying away from “those” sites has helped users avoid malicious code for a long time, but now thanks to a few black market tool kits users can be exposed to malware attacks from legitimate and trusted websites. This has become known as a drive-by attack, or ransomware, and virtually everyone is vulnerable. Below we are going to explain how this WordPress Hack works and what is a Ransomware.
Is your WordPress hacked?
[button url="https://fixmywp.com/wordpress-support-request"]Contact us for a free quote[/button]How the Ransomware WordPress Hack Works
As Dan Gooden explains in the article Mysterious spike in WordPress hack silently delivers ransomware to visitors, a large number of WordPress websites have recently been hacked to redirect visitors to a series of malicious sites. The sites host code from the Nuclear exploit kit that’s available from black markets across the Internet. The attacks exploit visitors that use out of date versions of software such as Microsoft Internet Explorer, Microsoft Silverlight, Adobe Reader, and Adobe Flash Player.
The code only infects first-time visitors and redirects them through a series of sites before they reach the malicious site. Their computers will then be infected with the Teslacrypt ransomware package – a program that will encrypt the users’ files so they can’t use them and holds them ransom until they pay for an expensive encryption key that will release them.
Malwarebytes Senior Security Researcher Jérôme Segura explains "WordPress sites are injected with huge blurbs of rogue code that perform a silent redirection to domains appearing to be hosting ads." He further explains "This is a distraction (and fraud) as the ad is stuffed with more code that sends visitors to the Nuclear Exploit Kit."
Andra Zaharia, a Marcom Manager at Heimdal Security, warns in the article Security Alert: Ransomware Delivered by Hundreds of Compromised WordPress Websites, that hacked websites are being redirected to a domain called “chrenovuihren”. There users see an advertisement that forces the traffic to the servers that host the Nuclear exploit kit.
Even though Google blacklisted many of the sites, Heimdal Security shows that the attackers may be refreshing old sites.
Hundreds of servers that host WordPress websites have been compromised. Heimdal has identified several IP addresses and domains that are active Nuclear gateways. The problem is the campaign uses several domains to deliver the malicious code and it can quickly change between them. They have identified 85 domains and they expect that number to grow.
Zaharia describes this as Teslacrypt ransomware. As she explains, “this Teslacrypt variant is identical to the other ransomware strains, so Cryptowall or other ransomware types could also infect the victim’s PC.”
Zaharia explains, “With fileless malware infections and commercially-available exploit kit, the cyber-crime scene is getting more complicated by the day.”
How is a WordPress Being Hacked by Ransomware?
According to Sucuri, the hacked sites include encrypted code at the end of each of the JavaScript files. It’s not clear how the WordPress websites are being infected with the malicious code. Possibilities include:
- Weak login credentials
- Vulnerable plugins
- The server’s OS
- An unknown exploit
The malware installs multiple backdoors on the webserver. Denis Sinegubko of Sucuri explains if users have multiple installations of WordPress on the same server then all of the domains will be infected through cross-site contamination. Cleaning one site, or even most sites, won’t solve the problem. Any site that’s not cleaned with re-infect all of the other sites. You’ll have to isolate, clean, and protect every site at the same time.
Protecting your Data Against the Attacks
One of the main problems with this security issue is antivirus programs might not protect end users. For example, in this test only two out of 66 antivirus programs detected the malicious code. Heimdal uses VirusTotal to keep an updated file of the full detection rate.
Here are some key recommendations to protect your data against ransomware:
- The best defense against these types of attacks is to install all security updates as soon as they are available.
- If you’re running Windows then run Microsoft's Enhanced Mitigation Experience Toolkit, a utility which helps prevent vulnerabilities in software from being exploited.
- Another good tool is the 64-bit version of Google's Chrome browser, which has enhanced security that uses more memory to build a larger haystack for Windows’ ASLR (address space layout randomization) that makes exploits harder to write.
- Use 2-Factor Authentication. This will strengthen your WordPress login against hackers.
- Force strong passwords. This will help ensure that you and your contributors’ logins are not too easy for hackers to guess.
- Keep your software and OS updated.
- Backup often and store the backups in multiple locations.
- Use a security tool that’s made to protect you against ransomware.
We’d like to hear from you. Have you been the victim of ransomware? How are you protecting your data? Do you have anything to add? Let us know in the comments.
Image credit: https://www.flickr.com/photos/132889348@N07/20012127713